
Upper Valley winter shelters kept dozens warm and dry
LEBANON — Organizers of two new emergency shelters, which kept dozens of Upper Valley residents off the streets this winter, are reflecting on the season and sorting out how to continue the service.Earlier this month, Lebanon’s emergency shelter for...

Woodstock boys lax defense steps up, holds off Hartford
WHITE RIVER JUNCTION — Monday night’s boys lacrosse game between host Hartford High and Woodstock came down to the final minute, with the Wasps prevailing, 11-10.The Vermont inter-division clash might have been decided, however, by a pair of goals at...
Sports

Pick a sport and Pete DePalo’s has probably officiated it over the past 40-plus years
Pete DePalo spent his first 15 years living on Coney Island in the New York City borough of Brooklyn, home of America’s first large-scale amusement park. His family moved to the Upper Valley and his life since has been filled with games.Soccer games....
 Lebanon girls lacrosse prevails over Coe-Brown
Lebanon girls lacrosse prevails over Coe-Brown
 Local roundup: Lebanon softball sweeps wins from Souhegan, Stark
Local roundup: Lebanon softball sweeps wins from Souhegan, Stark
 2024 Upper Valley high school tennis guide
2024 Upper Valley high school tennis guide
 2024 Upper Valley high school softball guide
2024 Upper Valley high school softball guide
Opinion

A Yankee Notebook: An inevitable and terminal move
Living three and a half hours apart, as we do, my dear friend Bea and I get to see each other about every two weeks or so, on average. This is almost without doubt an ideal arrangement, as our lifestyles are quite different, and neither of us could...
 Editorial: Gambling tarnishes America’s sporting life
Editorial: Gambling tarnishes America’s sporting life
 By the Way: A white nationalist’s many mistruths
By the Way: A white nationalist’s many mistruths
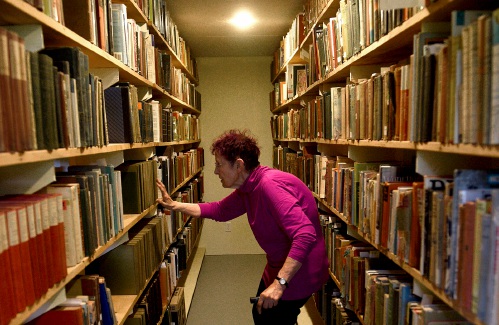 Column: The age-old question of what to read
Column: The age-old question of what to read
 Editorial: Transparency wins in NH Supreme Court ruling
Editorial: Transparency wins in NH Supreme Court ruling

Photos

Preserving habitat in Etna
 Pitching in
Pitching in
 Picture day prep
Picture day prep
 Helping a good cause in Etna
Helping a good cause in Etna
 Spring cleaning
Spring cleaning
Arts & Life

How a hurricane and a cardinal launched a UVM professor on a new career path
Before Hurricane Katrina hit her newly adopted city of New Orleans in 2005, Trish O’Kane knew next to nothing about the environment — let alone birds.O’Kane had spent much of her life working as an investigative human rights journalist in Central...
 Out & About: Vermont Center for Ecostudies continues Backyard Tick Project
Out & About: Vermont Center for Ecostudies continues Backyard Tick Project
 Art Notes: After losing primary venues, JAG Productions persists
Art Notes: After losing primary venues, JAG Productions persists
 Over Easy: Marvels in the heavens, and in the yard
Over Easy: Marvels in the heavens, and in the yard
Obituaries
 Jane Elizabeth Rooney
Jane Elizabeth Rooney
Manchester, NH - Jane Elizabeth Rooney, who had a long career as a social worker and psychotherapist, died on March 28, 2024, at Mount Carmel Rehabilitation and Nursing Center in Manchester, NH. Jane was born in Framingham, Massachuset... remainder of obit for Jane Elizabeth Rooney
 Cory John MacElman
Cory John MacElman
Lebanon, NH - Cory John MacElman, age 39, passed Friday, April 19, 2024. Ricker Funeral Home of Lebanon, NH is assisting the family. ... remainder of obit for Cory John MacElman
 Michael F. Hoar
Michael F. Hoar
Enfield, NH - Michael F. Hoar, 75, passed away following a period of declining health on Sunday April 21st 2024. He was born to the late Francis & Rita (Frazer) Hoar and was raised in Stoneham, MA. Michael was an avid skier and had work... remainder of obit for Michael F. Hoar
 Russell Haviland
Russell Haviland
West Newbury, VT - Russ Haviland passed away peacefully in North Haverhill, New Hampshire on April 18, 2024. He was born on March 17, 1941, in Brattleboro, Vermont to E. Randall Haviland and Gretchen (Shaw) Haviland. Russ's time was a l... remainder of obit for Russell Haviland


 Republicans have made illegal immigration a top issue in NH — sometimes with misinformation
Republicans have made illegal immigration a top issue in NH — sometimes with misinformation
 Owner of Friesian horse facility ordered to pay care costs for seized animals
Owner of Friesian horse facility ordered to pay care costs for seized animals
 Former principal of South Royalton School released from prison
Former principal of South Royalton School released from prison
 Upper Valley residents among advocates for NH aid-in-dying bill
Upper Valley residents among advocates for NH aid-in-dying bill
 Some families find freedom with Newport microschool
Some families find freedom with Newport microschool A Life: For Kevin Jones ‘everything was geared toward helping other people succeed’
A Life: For Kevin Jones ‘everything was geared toward helping other people succeed’ Editorial: Chris Sununu’s moral vacuum
Editorial: Chris Sununu’s moral vacuum
 Amid financial difficulties, Lebanon-based Revels North cancels midwinter show
Amid financial difficulties, Lebanon-based Revels North cancels midwinter show 
